Vault
Vault is a centralized custom solution by Hashicrop, to manage secret that provides:
-
A database to securely storing secrets.
-
A unified interface to any secret.
-
Tight access control based on policies.
-
A detailed audit log.
-
Knowing who is accessing what secret.
-
Several authentication methods to access it.
This plugin provides a possibility to fetch secrets from a Vault server and use them as Rudder variables directly on the agent. For security purpose, the Rudder server itself does not need to have access to the Vault.
Installation
-
You’re supposed to already have your Vault server installed and configured, also configured with secrets that can be any of the following types: SSL certificates and keys for your organization’s domain, credentials to connect to a corporate database server.
-
You must download and install the plugin from the repository with the rudder-pkg tool on your Server Rudder.
rudder package install-file <path to the rpkg>
Or if you have an active subscription :
rudder package install rudder-plugin-vault
-
Edit the configuration file in
/var/rudder/plugin-resources/vault.jsonon each agent. This config file must contain the address of your Vault server, credentials to access it based on the auth mode you want to use. A sample config is inshare/plugins/vault/sample_vault.json.
Usage
Use the Variable from Vault generic method in Rudder to fetch secrets.
Make sure the agents the generic method is being used on have a proper vault.json configuration.
A sample config is provided at /opt/rudder/share/plugins/vault/sample_vault.json.
This file needs your Vault server address, the configuration for at least one auth mode, and the name of the auth mode to be used.
Auth modes can be: token, userpass.
Example of usage :
-
Secret definition via Vault Web Interface:
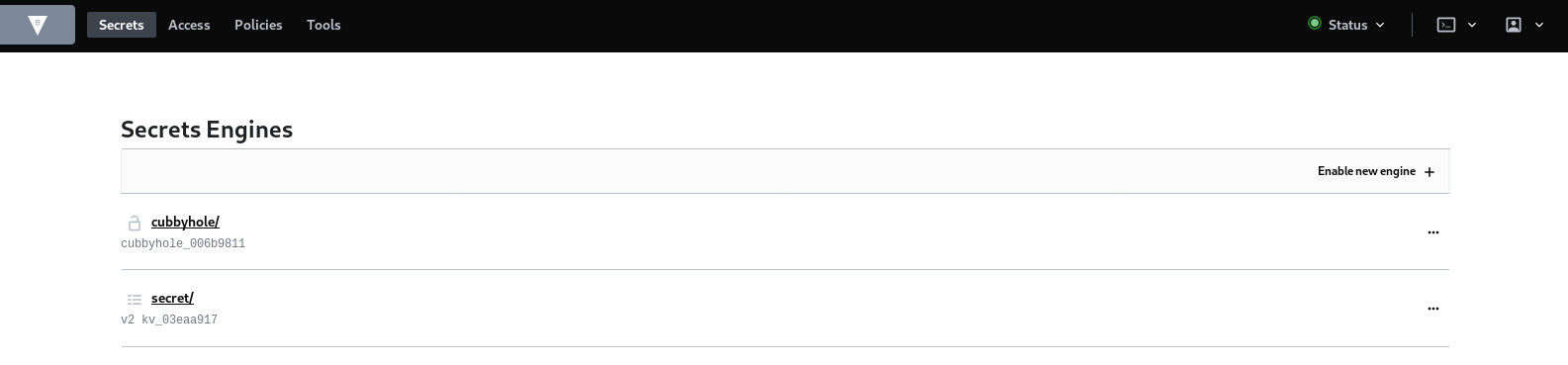
Start by creating the secret for the database server login information by clicking on the already defined secret engine for the key and value storage which is /secret:
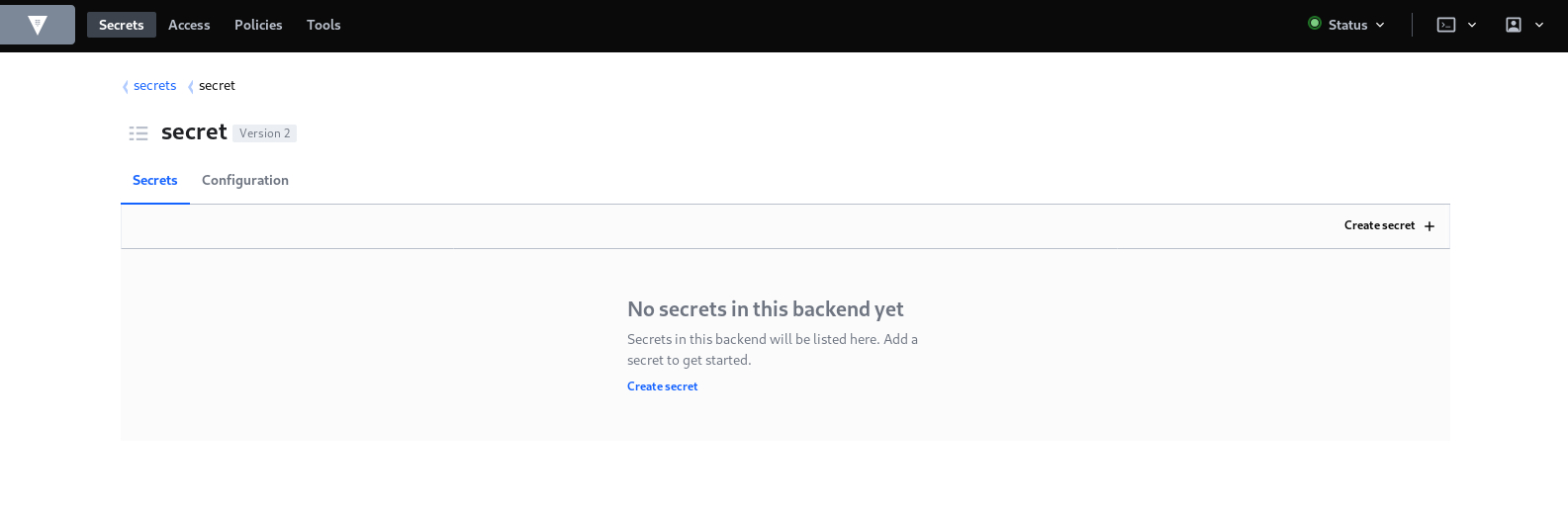
Then click on creating secret:
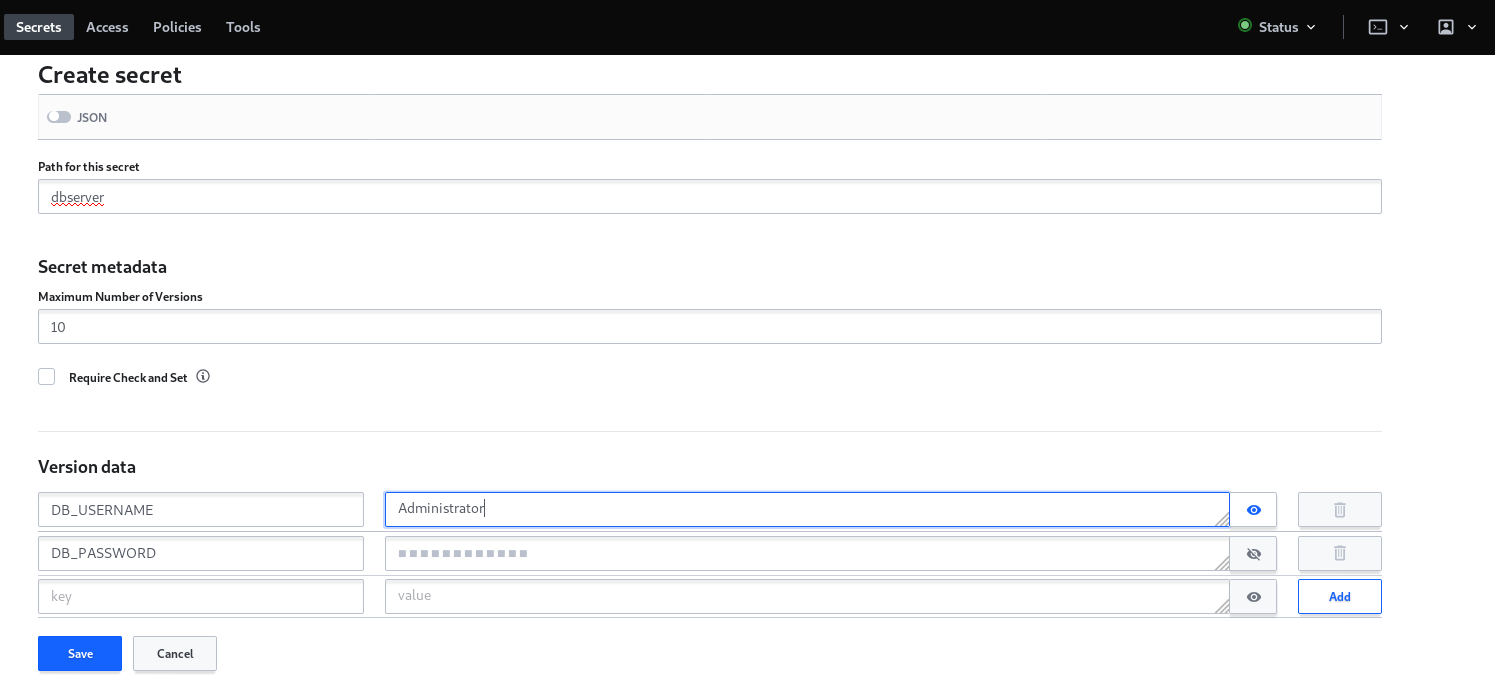
Now you have to set the parameters for your secret, which are basically the path (in other words the name of the secret), the number of versions and most importantly the key values parameters:
-
Secret fetching via Rudder Server technique editor:
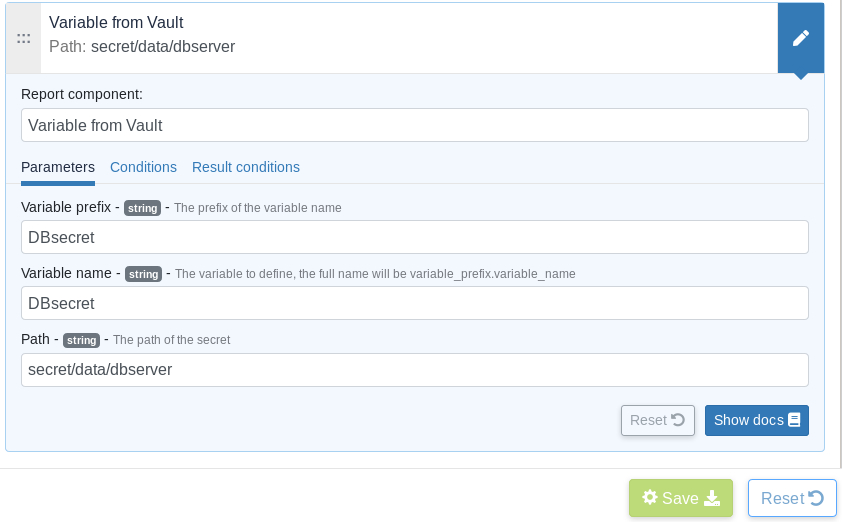
Finally you need to define the generic method on the rudder technique editor, the most important parameter is the path to the secret which needs to include /data
so it can retrieve the key and value that are defined under the secret name.
← Windows GLPI →